ZTX Framework
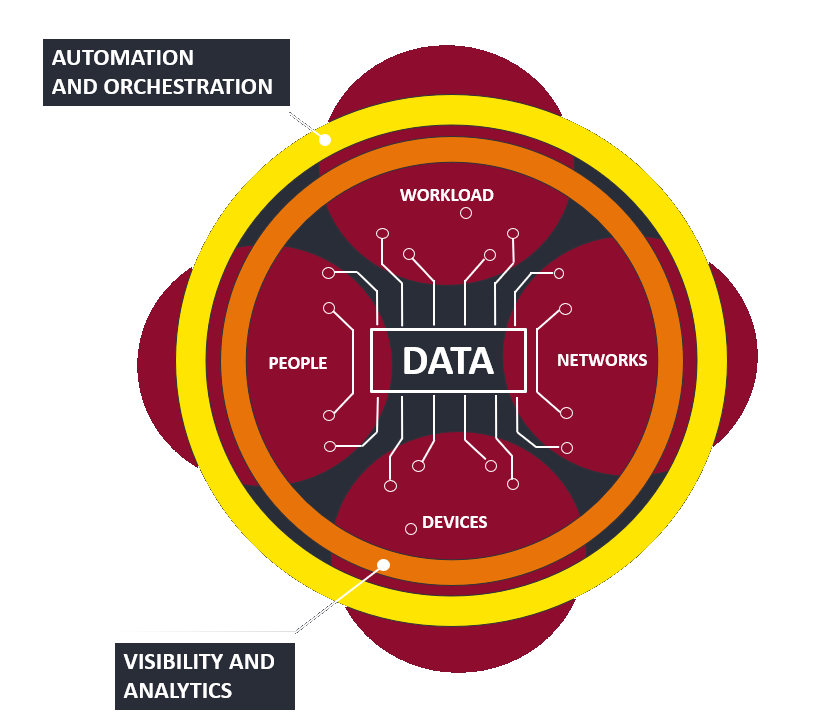
Zero Trust DNA
- Establishes security competencies across seven key areas: data, networks, people and workforce (human stakeholders), workloads and applications, devices, security visibility and analytics, and security automation and orchestration.
- A Zero Trust approach to security, security architecture, and operations becomes workload-first, data-driven, and identity-aware rather than static and perimeter-based.
- Empower & secure digital transformation
- Intelligent Security for complex environment
- Eliminate security deficiencies & gaps
- Classic Perimeter based on Security Architectures become worthless with new Attack techniques & complexity: with the ZTX we manage & reduce trusting traditional architectures.
- Secure Mobility & Cloud solutions, Monitor and protect Data, control user access and applications.

Steps To Achieve Zero Trust Information Security
- Zero Trust will be achieved differently for every organization based on how transactions flow through your business ecosystem and how employees, customers, and applications access data.
- Isolate and protect your extended network, enforce access control and inspection policies, and continuously monitor your Zero Trust ecosystem for signs of a breach or other malicious activity.

